Actionable “how-to’s” for bridging the tax tech gap

One of the biggest challenges facing tax leaders is the shrinking pool of qualified talent.
This guide explores how you can address the growing tax talent crisis through digital transformation, automation, and the integration of AI.
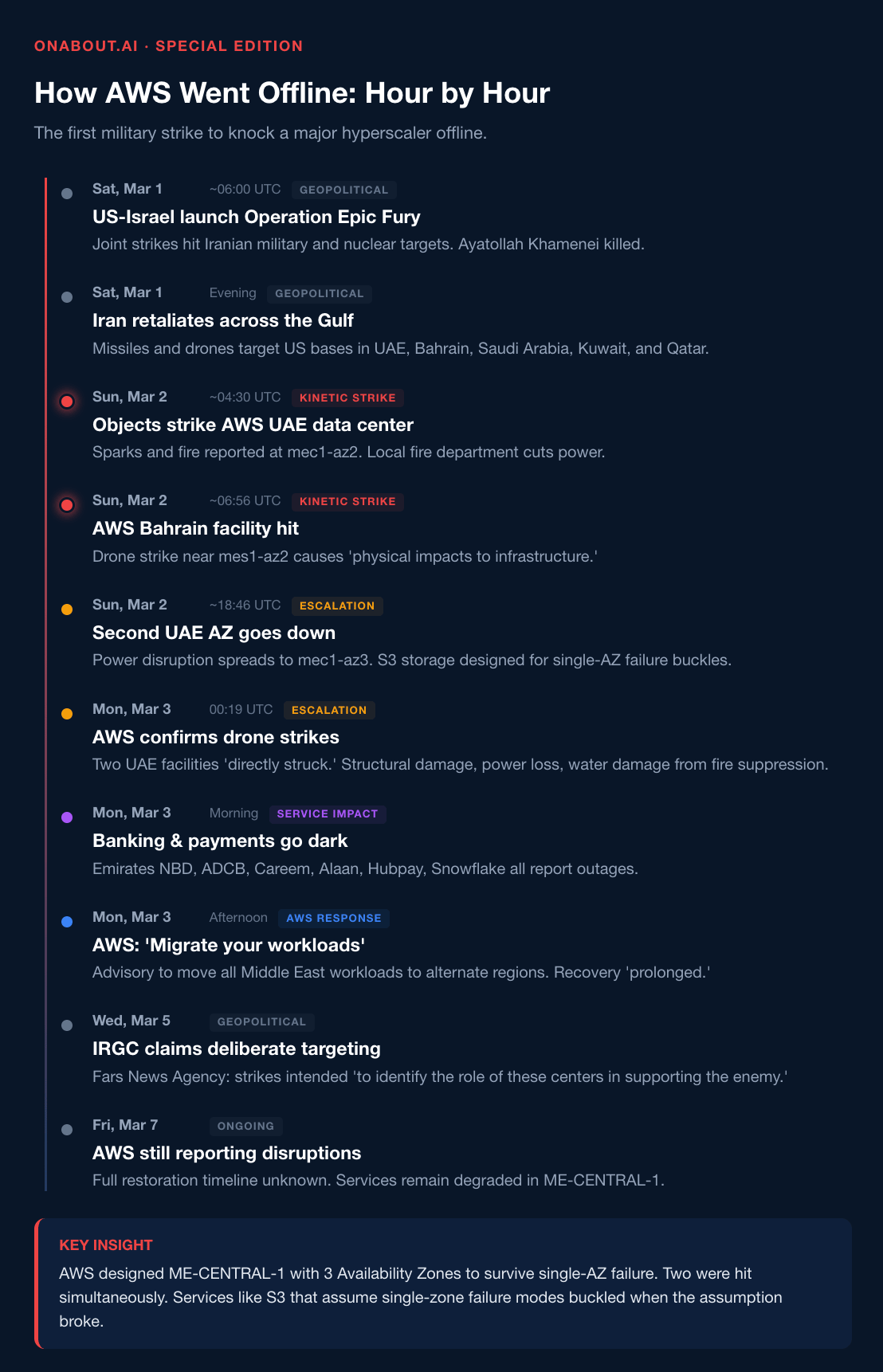
For twenty-five years, the cloud industry has operated on one foundational assumption: physical infrastructure is someone else's problem. You migrate your workloads, your provider handles availability, and your SLA guarantees uptime. On March 1, Iranian drones struck three AWS data centers across the UAE and Bahrain — and that assumption died in real time. Banking apps went dark. Payments froze. A government that had placed 85% of its data in a single cloud region discovered what concentration risk actually looks like. This is not a story about the Middle East. This is a story about every enterprise that treats cloud resilience as a checkbox instead of an architecture decision. Here's the full breakdown.
TL;DR
Iranian drones struck three AWS data centers in the UAE and Bahrain on March 1, marking the first military attack to knock a major hyperscaler offline. Banking, payments, and enterprise services across the Gulf went dark. AWS invoked force majeure. Your SLA won't save you. Here's what happened, why it matters for European infrastructure strategy, and what you should do this week.
What Happened
On Sunday, March 1, Iranian drone strikes hit three Amazon Web Services facilities across the Middle East. Two data centers in the UAE (ME-CENTRAL-1) were directly struck. A third facility in Bahrain (ME-SOUTH-1) was damaged by a nearby drone explosion. The strikes came as part of Tehran's retaliatory campaign following the joint US-Israeli Operation Epic Fury against Iran.
The damage was physical: structural collapse, power disruption, fires, and water damage from suppression systems. Two of three Availability Zones in the UAE region went down. Over 109 AWS services were degraded or offline.
Iran's Islamic Revolutionary Guard Corps later claimed the strikes were deliberate — aimed at probing the role of these facilities in supporting US military and intelligence operations.
As of this weekend, full services have not been restored. AWS continues to advise customers to migrate workloads out of the region entirely.
The Fallout
The downstream impact was immediate and severe.
Banking platforms went dark. Emirates NBD, Abu Dhabi Commercial Bank, and First Abu Dhabi Bank all experienced mobile app and phone banking outages. Payments platforms Alaan and Hubpay went offline. Ride-hailing and delivery giant Careem was knocked out across the UAE. Enterprise SaaS providers including Snowflake reported disruptions tied to the AWS outage.
Bahrain had migrated approximately 85% of its government data to the AWS Bahrain region since 2019. That's not a cloud strategy — that's a single point of national failure.
The strategic irony is hard to miss. The Gulf states poured billions into positioning themselves as the world's next AI and cloud hub. Cheap energy, cheap land, tax incentives — the pitch was compelling. The pitch did not account for drones.
What Your SLA Actually Says
Here's the part most CIOs haven't read carefully enough.
Every major AWS service agreement — EC2, S3, DynamoDB, Lambda — contains identical language excluding force majeure events from uptime commitments. The wording is broad: "factors outside of our reasonable control, including any force majeure event." War, terrorism, natural disasters — all explicitly excluded.
Translation: AWS promises 99.99% uptime, but that promise evaporates when the disruption is caused by something they can't control. Drone strikes on your data center qualify. Your service credits are worth nothing. Your disaster recovery plan is the only thing standing between you and an outage.
As one cloud law specialist put it: most customers treated their cloud service agreements as low-risk commodity purchases. They are not.
Action item: Pull your cloud provider SLAs this week. Read the force majeure clause. Read the exclusions. Read the limitation of liability. If you're running critical workloads in a single region — anywhere, not just the Middle East — you are carrying unpriced risk.
The European Lens
This is where the story gets personal for European enterprises.
Europe has spent years building a regulatory framework around data sovereignty, operational resilience, and infrastructure independence. The EU AI Act, DORA, NIS2, and the Digital Operational Resilience framework all push the same direction: know your dependencies, stress-test your assumptions, plan for the worst.
The AWS strikes just provided the stress test nobody planned for.
Consider the uncomfortable parallels:
Concentration risk is not a Middle Eastern problem. Ireland's data centers consume over 20% of national electricity. Amsterdam and Frankfurt have multi-year wait times for new power connections. The hyperscaler regions that host the majority of European enterprise workloads are concentrated in a handful of geographies — any of which could face disruption from conflict, energy crises, or regulatory action.
Multi-region is not multi-resilient. AWS's own architecture demonstrated this. ME-CENTRAL-1 was designed with three Availability Zones. Two went down simultaneously. Services like S3 that are designed to survive a single AZ failure buckled when two zones were hit. If your DR plan assumes single-zone failure, you're planning for the wrong scenario.
Data sovereignty is not just about jurisdiction. The Bahrain government put 85% of its data in a single cloud provider's single region. Sovereignty means nothing if physical destruction removes access to your data. The European conversation about data residency requirements needs to expand to include physical resilience — not just legal jurisdiction.egion — anywhere, not just the Middle East — you are carrying unpriced risk.
The New Risk Model
This event introduces a category that most enterprise risk frameworks don't account for: kinetic risk to cloud infrastructure.
Before March 1, 2026, the physical security of hyperscaler data centers was treated as a solved problem. Fire suppression, redundant power, cooling systems, physical access controls — these are mature capabilities. Nobody was modelling military strikes.
Now they have to.
The Centre for Strategic and International Studies warned last year that adversaries could target data centers, energy infrastructure supporting compute, and fiber chokepoints in the Gulf region. That warning is no longer theoretical.
For European enterprises, the implications extend beyond the Middle East:
Fiber route diversity matters. International fiber routes and oceanic cable landings are limited. If routing infrastructure is impacted by strikes, it becomes difficult to shift compute load to new regions — even if those regions are unaffected. Europe's connectivity to the Middle East, Asia, and Africa runs through a small number of submarine cable chokepoints.
Data centers are now dual-use targets. Iran explicitly stated the strikes targeted Amazon's infrastructure because of its role supporting US military operations. The co-location of commercial and military-adjacent workloads in the same facilities creates targeting risk for civilian customers. European defence and intelligence agencies are increasingly using commercial cloud. This convergence creates risk.
Insurance and compliance frameworks will change. Expect operational resilience regulators — particularly under DORA in the EU — to start asking financial institutions about kinetic risk to their cloud providers. If your third-party risk assessment doesn't include physical threat analysis of your provider's data center locations, it will need to.
The CISO's Kinetic Risk Checklist
Here's what to do this week:
1. Audit your region dependency. Map every production workload to its AWS/Azure/GCP region. Identify any workloads running in single-region deployments. Flag anything in geopolitically exposed regions — not just the Middle East, but anywhere conflict risk exists.
2. Stress-test for multi-AZ failure. Your DR plan probably assumes one Availability Zone goes down. Test what happens when two go down simultaneously. Test what happens when the entire region is unavailable for a week.
3. Read your SLA exclusions. Pull the force majeure clauses from every cloud provider agreement. Understand what you're actually covered for — and what you're not.
4. Evaluate cross-provider failover. True resilience in a contested world may require workloads that can fail over not just across regions, but across providers. This is expensive and complex. But the cost of not doing it just became visible.
5. Add geopolitical risk to your cloud selection criteria. Region selection has historically been driven by latency, data residency, and cost. Add physical security posture, proximity to conflict zones, and fiber route diversity to the evaluation.
6. Brief your board. This is not a technical issue. This is a business continuity issue that the board needs to understand. The question is simple: if a kinetic event took out our primary cloud region for a week, what happens to the business?
So What?
For 25 years, the cloud industry has operated on the assumption that physical infrastructure is someone else's problem. You move your workloads to AWS, Azure, or Google, and the provider handles availability. Your SLA guarantees uptime. Your architecture spans multiple zones.
That assumption died on March 1 in the UAE.
The cloud is not abstract. It is concrete, steel, copper, fiber, and generators — sitting in a specific building, in a specific city, in a specific country, with specific geopolitical exposure. When drones hit that building, your 99.99% uptime guarantee hits zero.
For European technology leaders, this is the moment to take operational resilience seriously — not as a compliance checkbox, but as an existential business requirement. The regulatory frameworks are already there: DORA, NIS2, the AI Act's requirements for high-risk system availability. The AWS strikes just provided the case study that makes the abstract concrete.
Nobody else in the EU AI governance space is connecting these dots. The conversation about cloud infrastructure resilience just became a conversation about national security, corporate survival, and the physical limits of digital sovereignty.
Own this moment.
That’s it for today.
This is a special edition of OnAbout.AI. Regular editions publish every Thursday with analysis of European AI infrastructure, governance, and strategy.
If this landed in your inbox from a forward — subscribe here to get the full picture every week.
Joao | OnAbout.AI European AI infrastructure intelligence for technology leaders

